고정 헤더 영역
상세 컨텐츠
본문
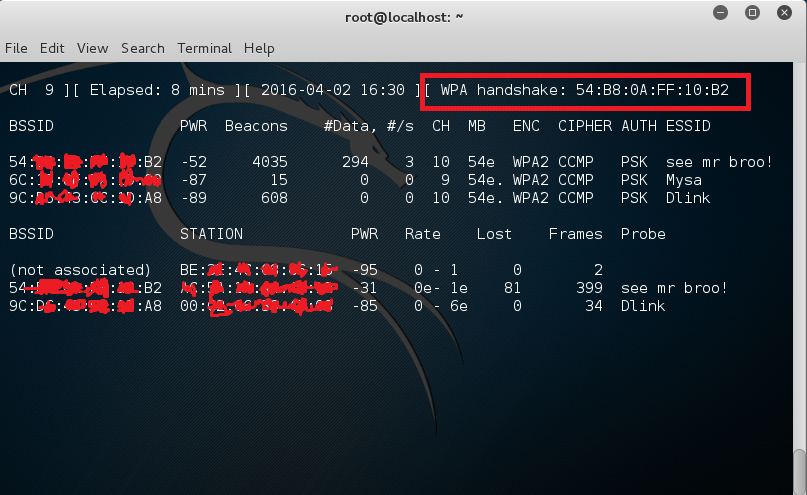
Reaver performs a brute force attack against an access point's WiFi Protected Setup pin number. Once the WPS pin is found, the WPA PSK can be recovered and alternately the AP's wireless settings can be reconfigured.
While Reaver does not support reconfiguring the AP, this can be accomplished with wpasupplicant once the WPS pin is known. Reaver performs a brute force attack against the AP, attempting every possible combination in order to guess the AP's 8 digit pin number. Since the pin numbers are all numeric, there are 10^8 (100,000,000) possible values for any given pin number. However, because the last digit of the pin is a checksum value which can be calculated based on the previous 7 digits, that key space is reduced to 10^7 (10,000,000) possible values. The key space is reduced even further due to the fact that the WPS authentication protocol cuts the pin in half and validates each half individually.
That means that there are 10^4 (10,000) possible values for the first half of the pin and 10^3 (1,000) possible values for the second half of the pin, with the last digit of the pin being a checksum. Reaver brute forces the first half of the pin and then the second half of the pin, meaning that the entire key space for the WPS pin number can be exhausted in 11,000 attempts.
The speed at which Reaver can test pin numbers is entirely limited by the speed at which the AP can process WPS requests. Some APs are fast enough that one pin can be tested every second; others are slower and only allow one pin every ten seconds. Statistically, it will only take half of that time in order to guess the correct pin number. Reaver WPA Cracking Tutorial.
Security researcher publicly disclosed a in the WPA2 encryption protocol today. Most devices and routers currently rely on WPA2 to encrypt your WiFi traffic, so chances are you’re affected. But first, let’s clarify what an attacker can and cannot do using the vulnerability. The attacker can intercept some of the traffic between your device and your router.
If traffic is encrypted properly using HTTPS, an attacker can’t look at this traffic. Attackers can’t obtain your Wi-Fi password using this vulnerability. They can just look at your unencrypted traffic if they know what they’re doing. With some devices, attackers can also perform and do some nasty things.
This vulnerability is like sharing the same WiFi network in a coffee shop or airport. The attacker needs to be in range of your WiFi network. They can’t attack you from miles and miles away. The attacker could also take control of a near you, but this is already a much more sophisticated attack. That’s why companies should release patches as soon as possible because chances are most attackers just learned about this vulnerability today. There’s at least a theoretical possibility that this vulnerability could be exploited by hackers to make it more scalable as an attack vector in future — thinking of, for example, how worms have been developed and released that spread from one insecure IoT device to another to build a zombie botnet. But currently this is not the case.
So here’s what to do now that the WPA2 protocol is vulnerable Update all the wireless things you own Good news! Your devices can be updated to prevent the KRACK vulnerability. Updated devices and non-updated devices can co-exist on the same network as the fix is backward compatible. So you should update all your routers and Wi-Fi devices (laptops, phones, tablets) with the latest security patches. You can also consider turning on auto-updates for future vulnerabilities as this won’t be the last one. Modern operating systems have become quite good at auto-updates.
Some devices (ahem Android) don’t receive a lot of updates and could continue to pose risks. The key point is that both clients and routers need to be fixed against KRACK so there are lots of potential attack vectors to consider. Look to your router Your router’s firmware absolutely needs updating. If the router has been supplied by your ISP, ask the company when their branded kit will be patched. If they don’t have an answer, keep asking. You can make sure your router is up-to-date by browsing the administration panel.
Find the user guide for your ISP-branded router and follow the instructions to connect to the admin pages. Latest Crunch Report. If your ISP is not quickly putting out a firmware update to fix KRACK, it may be time to consider switching your ISP. A less drastic option would be to buy a WiFi access point from a responsible company that has already issued a patch.
Wpa2 Hack
Plugging a WiFi access point into your ISP router and disabling WiFi on your ISP junk is a good alternative. Of some of the router makers that have already put out fixes (Ubiquiti, Microtik, Meraki, Aruba, FortiNet). Use Ethernet If your router doesn’t yet have a fix, and you don’t have a patched WiFi access point that could be used for wireless instead, you could Ethernet into your router and turn off its wireless function until it’s patched (assuming WiFi can be disabled on your router). Turn off WiFi on your device as well so that you’re sure all traffic goes through that sweet Ethernet cable.
If you still want to keep WiFi for some devices, consider switching to Ethernet for your essential devices. For instance, if you spend hours every day on a computer and use a ton of internet traffic from this computer, buy an Ethernet cable. Consider using cellular data on your phone Your phones and tablets don’t have an Ethernet port. If you want to make sure nobody is watching your traffic, disable WiFi on your device and use cellular data instead. This isn’t ideal if you live somewhere with a spotty network, pay extra for mobile data, or if you your telecom provider. Devices running Android 6.0 and later are more vulnerable than other devices.
It is trivially easy to perform a key reinstallation attack because of a bad implementation of the handshake mechanism in the WiFi stack. So Android users do need to be more careful.
What about Internet-of-Things devices? If you own a lot of IoT devices, consider which of those devices pose the most serious risk if unencrypted traffic is intercepted.
Say, for example, you own a connected security camera that doesn’t encrypt traffic when you’re on the same WiFi network — well, that could allow attackers to snoop on raw video footage inside your home. Take action accordingly — e.g. By pulling the most risky devices off your network until their makers issue patches. And be sure to keep an eye on the kinds of devices your kids might be connecting to your home network. At the same time, if an attacker can intercept traffic between your smart lightbulbs and your router, it’s probably fine.
What are they going to do with this information anyway? It’s fair to say that Edward Snowden wouldn’t want even info about how his lightbulbs are being turned on and off getting into the hands of a hacker, and with good reason.
But most people aren’t at risk of such an extreme level of state-sponsored surveillance. So you should determine your own level of risk and act accordingly. That said, the Internet of Things does have a when it comes to security.
So this could be a good moment to audit your connected device collection and consider junking any WiFi device whose makers don’t quickly issue a patch — they could pose some form of long term risk to your network. Install the HTTPS Everywhere extension As mentioned above, you can mitigate risks by prioritizing encrypted internet traffic over unencrypted traffic. The EFF has released a neat browser extension called. If you’re using Google Chrome, Firefox or Opera, you should considering installing the extension.
There’s no need to configure it, so anybody can do it. If a website offers unencrypted access (HTTP) and encrypted access (HTTPS), the extension automatically tells your browser to use the HTTPS version to encrypt your traffic.
If a website still relies exclusively on HTTP, the extension can’t do anything about it. The extension is no use if a company has a poor implementation of HTTPS and your traffic isn’t really encrypted. But HTTPS Everywhere is better than nothing. Don’t rely on a VPN as a solution On paper, using sounds smart. But we’ve been there already — be careful with VPN services out there. You can’t trust any of them.
When you use a VPN service, you reroute all your internet traffic to a VPN server in a data center somewhere. An attacker can’t see what you’re doing on your WiFi network, but a VPN company can log all your internet traffic and use it against you. For instance, The Register last week in a legal document that PureVPN shared key information with authorities to track and arrest a man.
And yet, the company’s website claims that PureVPN doesn’t keep any log. Again, don’t trust any VPN company.
Unless you’re willing to, a VPN service is not the solution. Especially paranoid?
Wpa2 Wifi Crack
Move to the woods For the most paranoid out there, who don’t want to/can’t stop using WiFi entirely, it may be time to relocate to a remote cabin in the woods far from any neighbors/wardrivers. Tech CEOs’ version of this privacy preserving strategy is to and knock them down to minimize the risk of any of their personal data being snooped on. Obviously this strategy is very expensive. Featured Image: wackystuff/ UNDER A LICENSE.




